|
||||||||||
You may redistribute this newsletter for non-commercial purposes. For commercial use contact jack@ganssle.com. To subscribe or unsubscribe go here or drop Jack an email. |
||||||||||
| Contents | ||||||||||
| Editor's Notes | ||||||||||
|
Tip for sending me email: My email filters are super aggressive and I no longer look at the spam mailbox. If you include the phrase "embedded muse" in the subject line your email will wend its weighty way to me. The Embedded Online Conference is coming up in April. I'll be doing a talk about designing hardware and software for ultra-low-power systems (most everything one hears about this subject is wrong). The normal rate for people signing up in March is $190, but for Embedded Muse readers it's just $90 if you use promo code MUSE2023. The regular price goes to $290 in April, though the $100 discount will still apply. |
||||||||||
| Quotes and Thoughts | ||||||||||
To invent, you need a good imagination and a pile of junk. Thomas A. Edison |
||||||||||
| Tools and Tips | ||||||||||
|
Please submit clever ideas or thoughts about tools, techniques and resources you love or hate. Here are the tool reviews submitted in the past. Are you aware of electromigration? Though we think of ICs as elements with an almost unlimited life, they do wear out. A recent article claims that for every 10°C above 100°C their life falls in half. Most of us are not designing circuits that run that hot, but a little noodling with Black's equation suggests that mean time to failures is highly temperature dependent, even well below 100°C. Electromigration is a very complex topic, though, and it's not clear that it would be an issue for parts not made with bleeding-edge geometries. Regarding the recent Muse discussions about binary editors, Brian Cuthie passed along this interesting link to an open-source product. |
||||||||||
| Incrementing Build Numbers | ||||||||||
Bob Paddock sent along a nice way to manage build numbers. Normally I would format the make file with the PRE html tag so it looks like code, but Dreamweaver, my least favorite program, is gorking on this. Here's the idea from Bob:
|
||||||||||
| The Rust Language | ||||||||||
Brad Nelson is a fan of Rust, and has kindly sent this take on the language:
|
||||||||||
| Security by Fiat | ||||||||||
Despite many temptations to use the platform of the Muse as a place to rant about politics, I don't, and won't, unless perhaps in a future final issue I chose a Viking-like bit of virtual self-immolation before sailing off into the sunset. But. The US's current administration is (quite rightly) addressing the issue of infosec. They've issued a national cybersecurity document that is long on tropes but rather lacking in specifics. One paragraph, though, bears on the embedded space:
I'm not entirely sure what this word-salad means. It appears that developers, or at least their organizations, will be held accountable for insecure code. Unless, that is, that they conform to some unknown "standards" that I cannot imagine being specific enough to mean much. There have been some examples of legislation leading to great code. Commercial avionics generally must conform to DO-178C, and, in general (yes, there have been a very few notable exceptions) the results have been impressive. And yet, we really don't know if that's due to the requirements of the standard, or to a culture that embraces safety at any cost. The most critical avionics resembles embedded systems of years ago. Unconnected, some hacker in one of the 'Stans is not a problem. Now, when practically any net-connected transistor is a threat vector the most innocuous of products can be a gateway to chaos. Though I appreciate an effort to address these issues, it's hard to see a way forward that works. Alas, "works" has to include market forces as products are made to be sold. Security costs money. When our perfectly-engineered device competes against one from China at half the cost with ten times the vulnerabilities, it's hard to see how we can be successful. In many industries regulation works. The MGM Grand Hotel inferno in 1980 killed 85 people. Management failed to spend $192,000 to install a sprinkler system, as the code at that time did not require one. Estimates pegged the cost of the fire at a cool billion dollars. Today, the code would never permit a hotel without sprinklers. But I just don't see a practical way to mandate secure code. And even the best software still has an obvious failure mode: users. Social engineering is pretty difficult to overcome. |
||||||||||
| Failure of the Week | ||||||||||
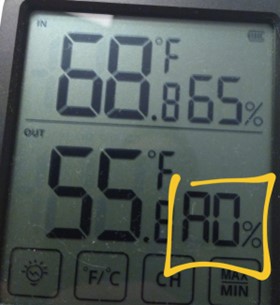
Harold Kraus sent this anomaly: And this bit of fun is from Thomas Osbrink: Have you submitted a Failure of the Week? I'm getting a ton of these and yours was added to the queue. |
||||||||||
| Jobs! | ||||||||||
Let me know if you’re hiring embedded engineers. No recruiters please, and I reserve the right to edit ads to fit the format and intent of this newsletter. Please keep it to 100 words. There is no charge for a job ad.
|
||||||||||
| Joke For The Week | ||||||||||
These jokes are archived here. Einstein, Newton, and Pascal decide to play hide-and-seek. Einstein is "It," closes his eyes, counts to 10, and then opens them. |
||||||||||
| About The Embedded Muse | ||||||||||
The Embedded Muse is Jack Ganssle's newsletter. Send complaints, comments, and contributions to me at jack@ganssle.com. The Embedded Muse is supported by The Ganssle Group, whose mission is to help embedded folks get better products to market faster. |