|
|
||||||||
You may redistribute this newsletter for non-commercial purposes. For commercial use contact jack@ganssle.com. |
||||||||
| Contents | ||||||||
| Editor's Notes | ||||||||
|
||||||||
| Quotes and Thoughts | ||||||||
Harold Kraus sent in this quote from Jessica Keyes: "Automating a money-losing process allows you to lose more money faster and with greater accuracy." |
||||||||
| Tools and Tips | ||||||||
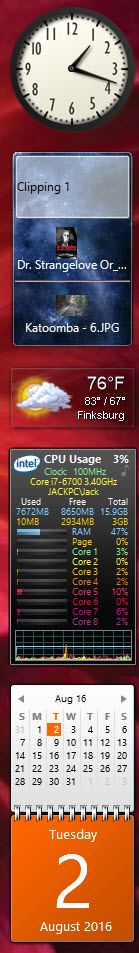
Please submit clever ideas or thoughts about tools, techniques and resources you love or hate. Here are the tool reviews submitted in the past. Gary Kildall of Digital Research and CP/M fame wrote a manuscript about his life that has long been available only to his immediate family. His children have recently made portions of it available to the public. You can get it from here. I'm a fan of the Ada language, and AdaCore is sponsoring a Make With Ada contest. There's more info here. The top prize is 5000 Euros. Full disclosure - I'm one of the judges. It could be a lot of fun to build something with a Cortex-M MCU. As noted later in this Muse, I had to replace my desktop computer recently and am now running Windows 10. So far, no real complaints. As part of setting up this machine I loaded one of my favorite free mini-applications, 8GadgetPack, which, it turns out, is new and improved from the last time I loaded it. This is a free collection of dozens of little bitty apps. You select the ones you want and then they live on the right-hand side of your screen. Here are the ones I use:
The function of each of these is mostly obvious. The second one down is a clipboard expander. Every time you copy something (including pictures, movies, etc.) to the clipboard it also goes to this app. Then use the mouse's scroll bar to select a particular clip, click once on it, and now that clip is the active one that will get pasted when you select "paste" or hit control-V. Very handy. Carl Peterson wrote:
|
||||||||
| Freebies and Discounts | ||||||||
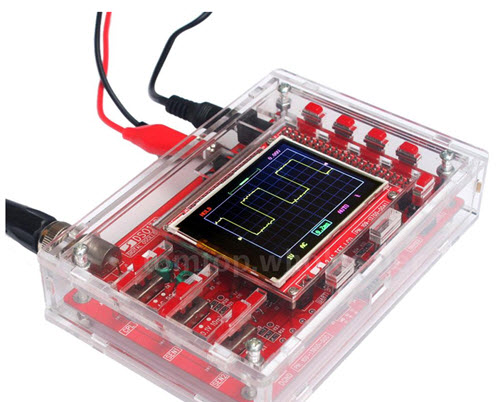
This month's giveaway is a 200 KHz oscilloscope in kit form, without the 9 V power supply. Again - you have to solder this together. This is a real entry-level unit but looks like fun.
Enter via this link. |
||||||||
| A Backup Strategy | ||||||||
If my computers were stolen or lost in a fire the insurance company would make me whole. But if my data disappeared I'm out of business. Or out of memories if those thousands of pictures and other digital memorabilia disappeared. Yet hard drives fail. Ransomware can encrypt your files; a new, nastier version pretends to encrypt but actually deletes everything. Fires happen as does theft. Accidental deletions are common. How do you back up your files? We have a small network here with new content being generated on only a few computers. But we have a fortress-like approach to backups which has been very effective. Here's our approach. One computer is the designated "master." It controls all of the backups. It's a Windows machine running the $30 utility SecondCopy, which automatically starts every morning at 3. One of the program's advanced options is to start external programs before and/or after SecondCopy does its work. In our case it starts a batch file that XCOPYs changed/new files from the other computers on the network to the master machine. XCOPY's /y, /d and /s options are used. The results are appended to a log file for troubleshooting. All of that data, the original and backups, is on the master computer which could be lost via fire or other calamity. So there are two USB external drives. One lives in a secure offisite location. Every Friday Outlook's task manager tells me to swap the two drives. If we had a fire we could lose a week's data, which for us isn't that much. We are building a new barn, and when that's done I plan to investigate using a disk antenna (the barn is 200 feet away) to wi-fi a backup computer there every night. Or I may lay some Cat 5 cable in the electric trench we will be digging. Every Friday, prior to swapping disks, I check the log file on the backup disks to ensure everything worked as intended. Autorecovery files in applications like Word are set to go to the second internal hard drive, so if the c: drive fails while editing a document changes to that document won't be lost. But what about ransomware? I don't know if it typically attacks all at once or can lie dormant before doing its dastardly deed. So when SecondCopy finishes it starts another batch file that changes the attributes of the backup directories on the USB drive to hidden and system. Those directories essentially disappear. Sure, attacking code could undo the attribute changes, but since the names of those backup directories are known only to us, this affords at least some level of protection. The batch file that runs before the backup changes the attributes back just for the duration of the SecondCopy's work. Many tout the cloud as a backup solution, and it can be effective. But there are perils. At least one provider lost most of their customers' data due to an attack. I don't want my personal info, even though the important stuff is encrypted, out in some mysterious cloud where you don't know where it is. Do deletions actually delete all copies? Who knows what agency might be sifting through it? Some of the privacy statements are horrifying - they're little more than notices that the providers will vacuum up everything. There was a good article in EETimes about cloud-based storage. We need a healthy digital paranoia to preserve the bits. |
||||||||
| The Internet of Evil Things | ||||||||
Teakettles, cameras, door locks, road signs, nuclear power plants - these and many more have been hacked and are listed in the Internet of Evil Things Hall of Shame here. Thanks to PhaedruS SystemS's newsletter for pointing this out. |
||||||||
| Monitoring Code | ||||||||
In response to Andrew Kollosche's idea for an activity meter in the last issue, Keith Lockstone wrote:
Along those lines, back in the dark ages we embedded Data General Nova minicomputers into systems. Debugging tools were primitive so we'd tune a shortwave radio to pick up the computer's EMI. The tones told us a lot about what the programs was doing. Mark Moulding sent in this:
Vic Plichota had a fun idea:
This is Paul Carpenter's approach:
There are a lot of commercial tools available for monitoring the code. I've used Micrium's uC/Probe and like it a lot. Percepio's TraceAlyzer is getting a lot of buzz lately, and Express Logic's TraceX looks great, too. |
||||||||
| Jobs! | ||||||||
Let me know if you’re hiring embedded engineers. No recruiters please, and I reserve the right to edit ads to fit the format and intent of this newsletter. Please keep it to 100 words. There is no charge for a job ad. | ||||||||
| Joke For The Week | ||||||||
Note: These jokes are archived at www.ganssle.com/jokes.htm. Two strings walk into a bar and sit down. The bartender says, "So what'll it be?" The first string says, "I think I'll have a beer quag fulk boorg jdk^CjfdLk jk3s d#f67howe%^U r89nvy owmc63^Dz x.xvcu" "Please excuse my friend," the second string says, "He isn't null-terminated." |
||||||||
| Advertise With Us | ||||||||
Advertise in The Embedded Muse! Over 27,000 embedded developers get this twice-monthly publication. . |
||||||||
| About The Embedded Muse | ||||||||
The Embedded Muse is Jack Ganssle's newsletter. Send complaints, comments, and contributions to me at jack@ganssle.com. The Embedded Muse is supported by The Ganssle Group, whose mission is to help embedded folks get better products to market faster. |





 s
s